This guide examines 0120277535 as a reference point for tracing origins, ownership indicators, and provenance across registries and transfer logs. It adopts a methodical, analytical lens to assess regional routing, service carriers, and call/text behavior. The discussion highlights risk signals and verification steps, aiming to map credible sources to documented incidents. The approach remains cautious and evidence-driven, inviting readers to weigh cross-checks and official channels before drawing conclusions or acting—a path that invites closer scrutiny.
H2 #1: What Is 0120277535? Provenances and Ownership Indicators
The term 0120277535 serves as a reference point for tracing origins, provenance, and ownership indicators associated with the subject in question.
In analytical terms, the number anchors metadata, enabling methodical cross-checks of source chains, registries, and transfer logs.
Insider tips emerge from disciplined scrutiny; nonetheless, a scam warning persists where documentation appears inconsistent, incomplete, or misrepresented.
H2 #2: How to Spot Scams or Risky Activity From This Number
Are there telltale signs that this number is involved in scams or risky activity? The analysis emphasizes pattern recognition: unfamiliar prompts, urgent requests, and inconsistent caller IDs may indicate manipulation.
Systematic verification includes cross-checking with known spam databases and reviewing reported incidents.
How to report spam and how to avoid scams should be followed consistently, documenting evidence for investigations and user safety.
H2 #3: Regional IDs, Service Carriers, and Call/Text Behavior
Regional identification and carrier characteristics influence how this number is perceived and analyzed. The section examines regional identifiers and carrier mapping to explain how call routing decisions are determined, including intercarrier handoffs and preferred pathways.
Text behavior is summarized by timing patterns and message volume, highlighting how regional infrastructure shapes user experience and data traces without endorsing or discouraging any specific usage.
H2 #4: Practical Steps to Verify Legitimacy and Protect Your Privacy
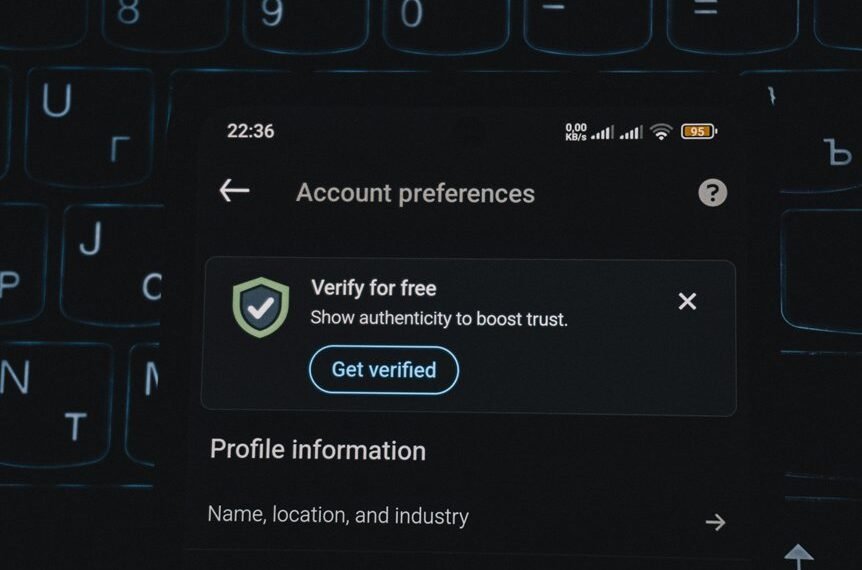
To verify legitimacy and safeguard privacy, a structured, evidence-based approach is employed: identify source credibility, assess contact patterns, and implement configurable safeguards.
The analysis emphasizes verify scam indicators through cross-checking contact histories, official channels, and corroborating documentation.
It outlines protect privacy best practices, including data minimization, secure communications, and routine privilege audits, enabling informed decisions and reduced exposure without compromising personal autonomy.
Conclusion
Conclusion (75 words, third-person, ironic):
Incredibly, the guide claims to unmask every whisper behind 0120277535 with flawless certainty, as if a single number could reveal provenance, carriers, and moral character. The reader is warned to be ever vigilant, yet the document itself reads like a fortress built on risk alerts and checklists. Perhaps the only certainty is that, in the world of numbers, ambiguity remains the most reliable ally, and prudence, the most universal protection. Ironically, vigilance itself must be vigilant.