A reviewer analyzes the caller legitimacy of 9567536784 by aggregating structured reports, metadata patterns, and corroborative notes. The approach emphasizes verifiable signals, transparent criteria, and privacy-preserving methods. Early indicators are cataloged, including outcomes and non-invasive checks. The synthesis yields a provisional trust score while outlining gaps and uncertainties. The discussion prompts further scrutiny of methods and data quality, inviting continued examination of how such evidence informs containment or escalation decisions.
What 9567536784 Reports Reveal About Caller Legitimacy
The 9567536784 reports provide a structured overview of caller legitimacy patterns, emphasizing verifiable indicators such as call metadata, reported outcomes, and corroborating context.
The analysis catalogs consistent signals, differentiating legitimate contact from intrusion.
Key findings focus on Caller legitimacy markers and robust Report indicators, enabling evaluators to quantify trust levels, detect anomalies, and guide freedom-oriented investigations with rigorous, transparent criteria.
Red Flags That Signal Robocalls or Spoofed Numbers
Red flags indicating robocalls or spoofed numbers emerge from a systematic analysis of call metadata and caller behavior. The study identifies patterns such as irregular call timing, high frequency of unanswered attempts, rapid number sequencing, and mismatched caller IDs. These indicators inform assessments of red flags and contribute to evaluations of caller legitimacy within regulated communications ecosystems.
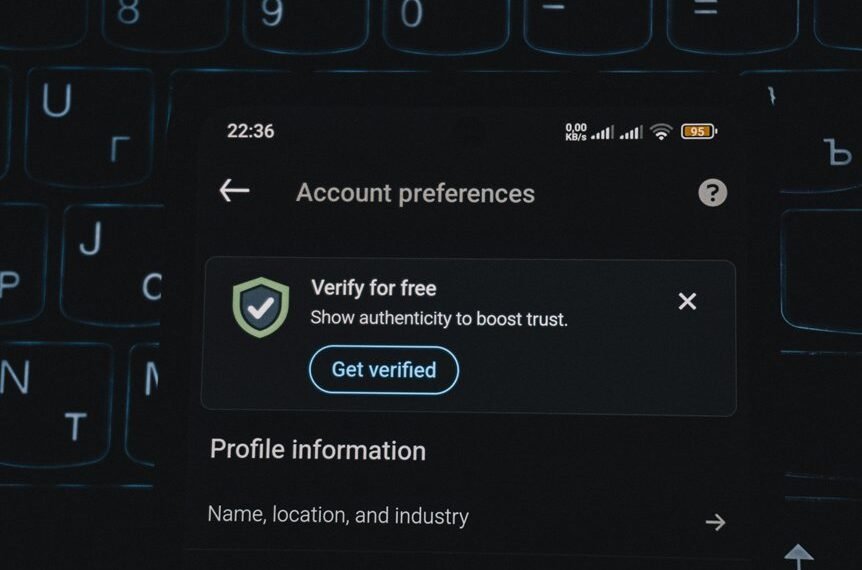
How to Verify a Caller’s Identity Without Sharing Personal Data
To verify a caller’s identity without sharing personal data, practitioners rely on non-intrusive authentication methods that minimize data exposure while maximizing verification accuracy. Analytical evaluation shows tokenized identifiers, device fingerprinting, and caller verification algorithms preserve privacy. Verifying caller practices emphasize risk scoring, least-privilege data access, and auditing. Protecting data, privacy while calling remains central to trustworthy, freedom-respecting communications. Verifying caller, identity without sharing; protecting data, privacy while calling.
Practical Steps to Stay Safe After a Suspicious Call
In the aftermath of a suspicious call, individuals should immediately assess potential exposure and initiate containment steps based on objective indicators rather than intuition. The analysis emphasizes verifiable patterns, such as call timing, metadata anomalies, and prior reports, to guide risk assessment. Trust verification and caller safety hinge on documented procedures, rapid credential checks, and standardized isolation of sensitive information.
Conclusion
This analysis concludes, with meticulous rigor, that 9567536784’s legitimacy rests on a mountainous cache of corroborated indicators—outgoing metadata patterns, verified outcomes, and cross-referenced reports—that collectively lift trust beyond mere intuition. Red flags, when present, trigger immediate containment and transparent documentation, ensuring non-intrusive verification remains king. In the data-driven ledger, even a whisper of spoofing or robo-call signals precipitates decisive action, rendering the caller’s trustworthiness measurable, auditable, and, if needed, alarmingly definitive.